Universal QR Infrastructure for Guest Safety, Fleet Logistics, and Enterprise Assets
QAAR provides a unified, encrypted platform to manage human emergency profiles (Guests, Students, Staff), recover high-value assets, and track global logistics with zero-knowledge security.
Create your secure profile
Engineered for Operational Safety, Recovery, and Institutional Support
QAAR automates the transition from a physical scan to a secure digital workflow—streamlining emergency response, guardian relay, asset recovery, and enterprise-scale incident management.
Safety & Medical Intelligence
Secure emergency identity for hotel guests, encrypted medical protocols for patients, and automated guardian relay for educational institutions.

Critical response when every second is a factor
QAAR bridges the gap between responders and stakeholders. Public safety data is instantly accessible, while sensitive identity and medical records remain secured within our zero-knowledge architecture until authorized for release.
Logistics & Asset Intelligence
Track corporate fleets, hotel valet operations, and IT inventory with real-time status updates and auditable proof-of-recovery.

Accelerated recovery with built-in auditability
Whether managing a corporate fleet, mobility gear, or botanical assets, QAAR eliminates the friction of recovery. Every scan triggers a traceable workflow, preserving privacy while providing owners with real-time status updates.
Governance & Smart-City Ready
Privacy-first, multilingual frameworks for municipalities and global organizations requiring traceable incident response.

Multi-tenant architecture for global operations
Built for institutional reliability, QAAR supports complex organizational hierarchies. Our platform allows government bodies and large enterprises to deploy secure QR workflows with granular permission controls.
Global Ecosystems & Strategic Verticals
A unified, encrypted infrastructure designed for rapid identification and secure data relay across diverse sectors.
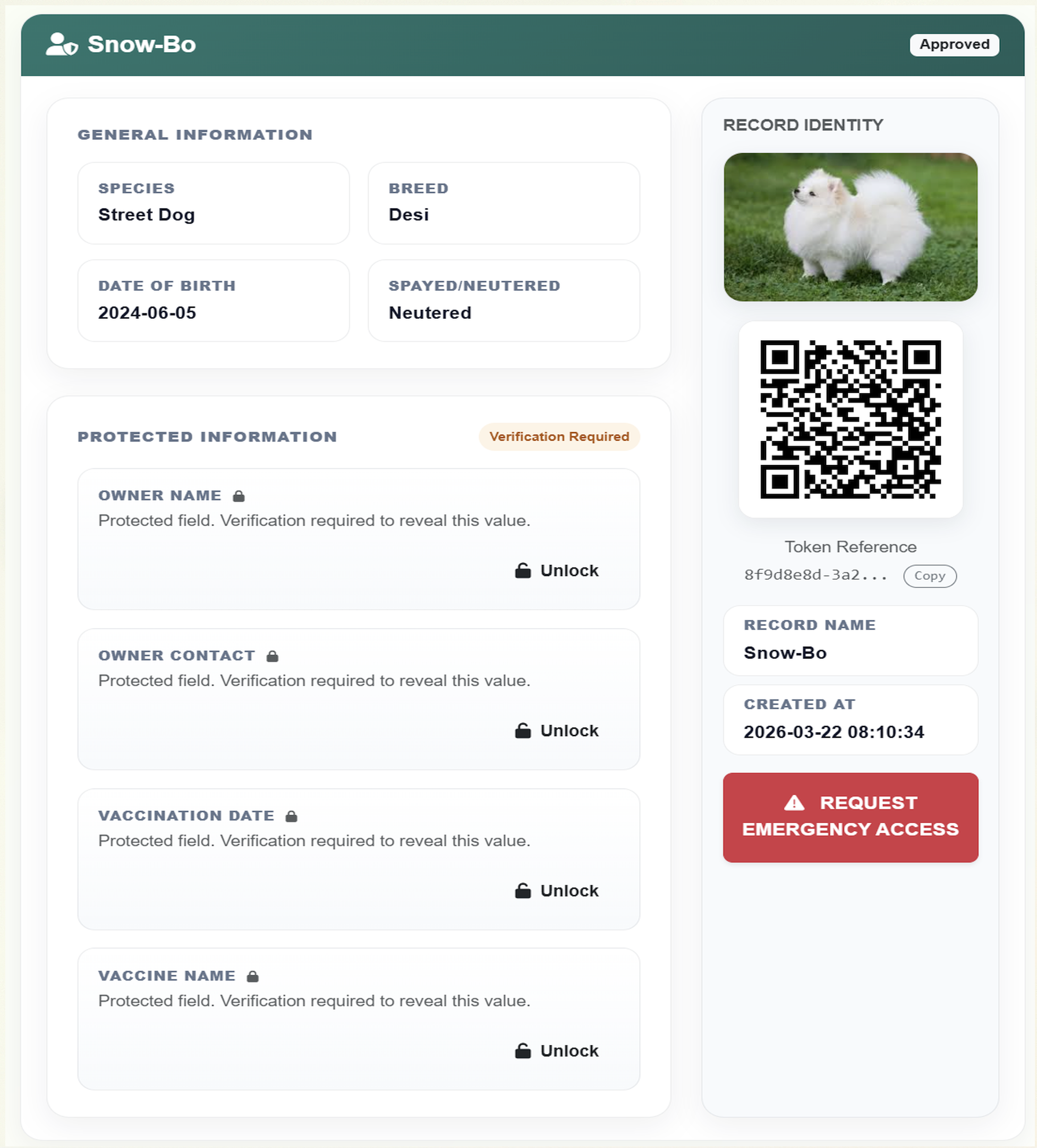
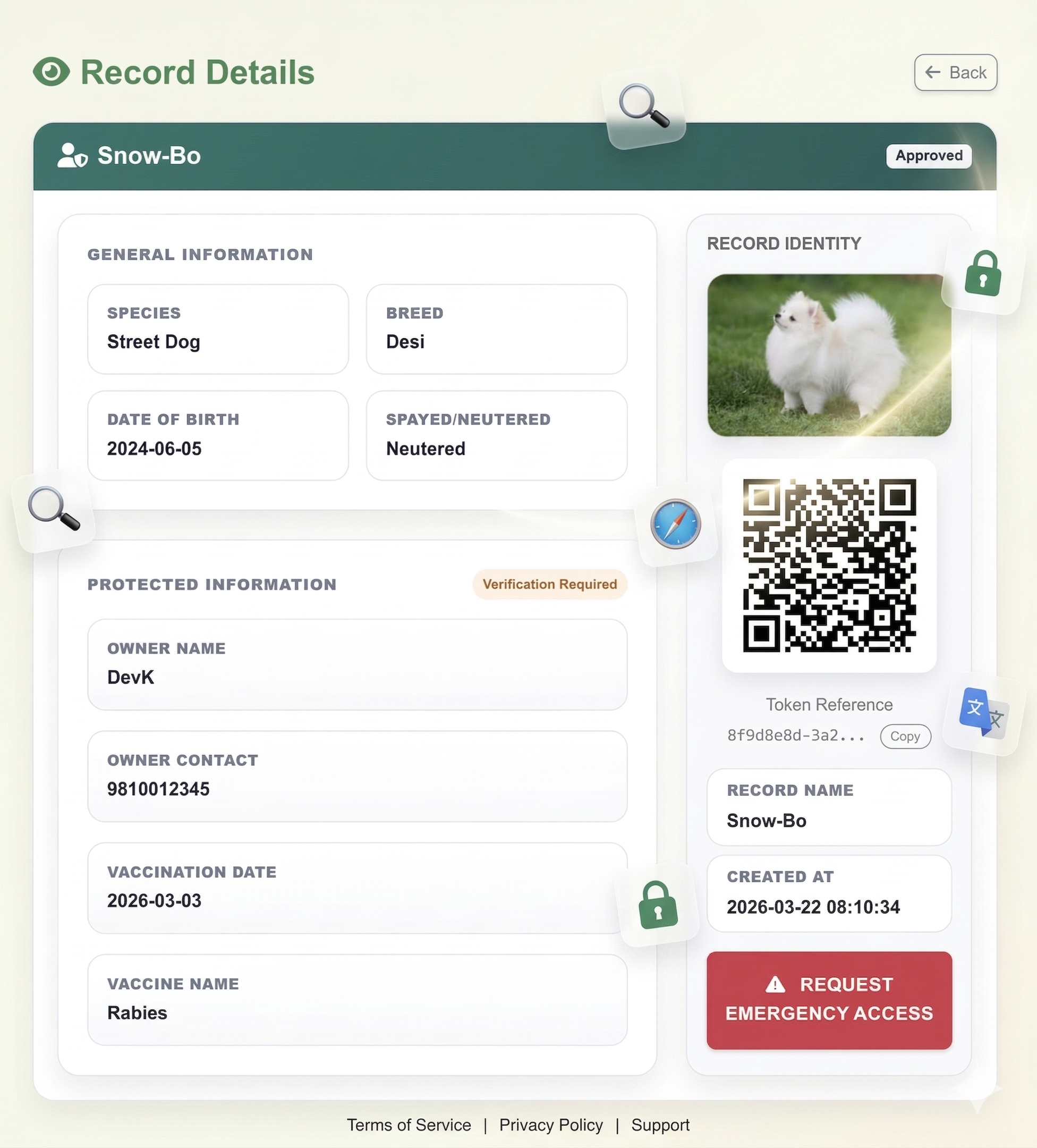
Individuals & Families
Secure emergency medical IDs, pet recovery tags, and private-relay contact for personal vehicles and high-value assets.

Unified Protection for What Matters Most
Provide instant access to emergency medical profiles, allow good Samaritans to return lost pets or items securely, and safeguard personal vehicles without exposing private contact information to the public.
Hospitality & Corporate
Guest emergency profiles, luggage tracking, visitor management, and employee safety protocols for global hotel chains and enterprises.

Scalable Workflows for Hospitality & Business
Equip your concierge with smart luggage tracking, manage facility visitors, and secure corporate assets with branded QR infrastructure. Every scan provides actionable data, role-based access, and detailed audit logs for compliance.
Institutional & Logistics
Patient identification, fleet logistics tracking, and municipal citizen-assistance programs for smart cities and healthcare providers.

Resilient Infrastructure for Health & Transit
Deploy robust, multilingual QR touchpoints across logistics fleets, hospital patient-wristbands, and civic infrastructure. Enable rapid identification, encrypted medical relay, and secure chain-of-custody tracking.
Your data is encrypted, locked, and under your control
QAAR utilizes advanced Application-Level AES-256 encryption. Sensitive data is mathematically scrambled before it ever reaches our databases, ensuring zero-knowledge storage.
AES-256 Encryption
Medical details, private contacts, and identification numbers are secured using military-grade symmetric encryption. The database cannot read your sensitive fields.
Dynamic Access Control
Protected data remains invisible to bystanders. Access requires explicit permission via dynamic OTPs (Email, SMS, WhatsApp) or secure user-defined passcodes.
Zero-Knowledge Vault
Our infrastructure separates the encryption keys from the storage servers. Even our system administrators cannot view your protected personal information.